The Real IT Problem
Even if your team can run Shibboleth internally, operational risks remain. Staff turnover, constant upgrades, and integration headaches can disrupt access and compliance.
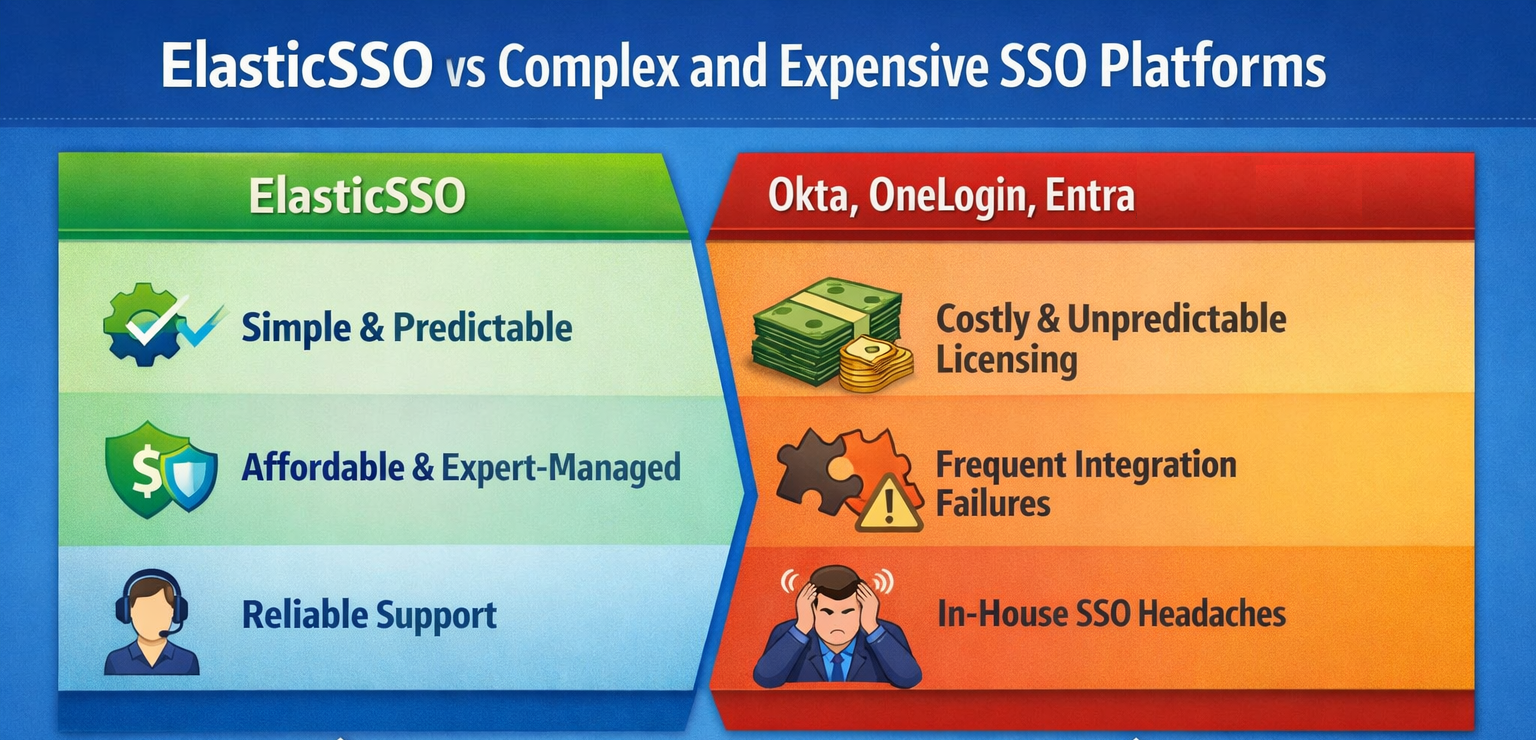
ElasticSSO vs Complex and Expensive SSO Platforms
- Okta, OneLogin, Entra are costly – unpredictable licensing
- Integrations often fail – SaaS and MFA workflows break
- In-house Shibboleth is risky – staff turnover & upgrades
Why CIOs & IT Directors Choose ElasticSSO
Hosted SSO Built for IT Simplicity
- SOC 2 and HECVAT compliant hosting – AWS or Azure
- Modular architecture – MFA, SIEM, directories
- Zero-downtime migration – Shibboleth or commercial SSO
- Scales across thousands of applications